Finder Wallet is not a bank. Terms and conditions apply. Crypto trading products are made available in the Finder App, powered by Finder Wallet Pty Ltd, an AUSTRAC registered Digital Currency Exchange (DCE). Trading and holding cryptocurrency has a high level of risk. Cryptocurrency is a volatile asset class. You can incur losses. You should only trade cryptocurrency or related products if you fully understand, and agree to, the risks. We suggest you seek independent financial advice prior to accessing our services.
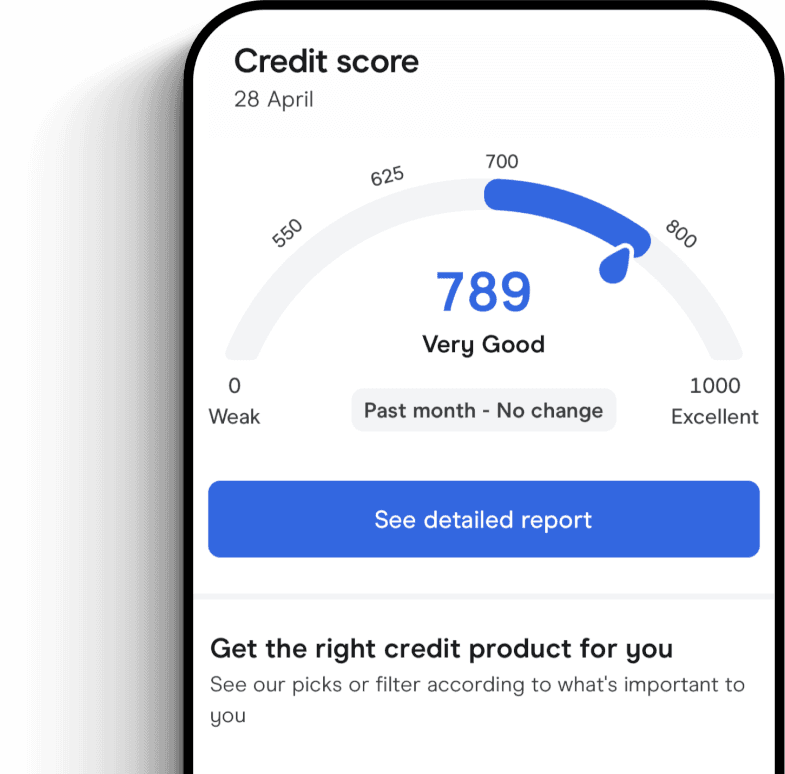
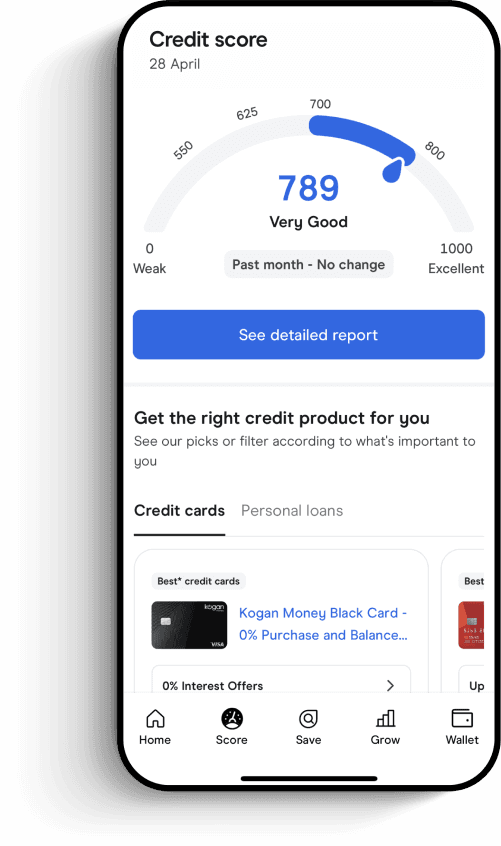
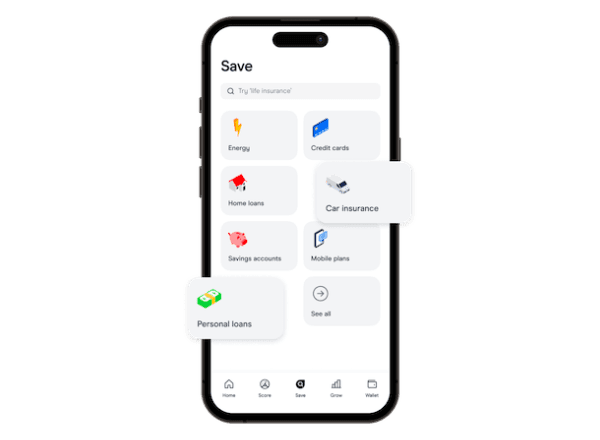
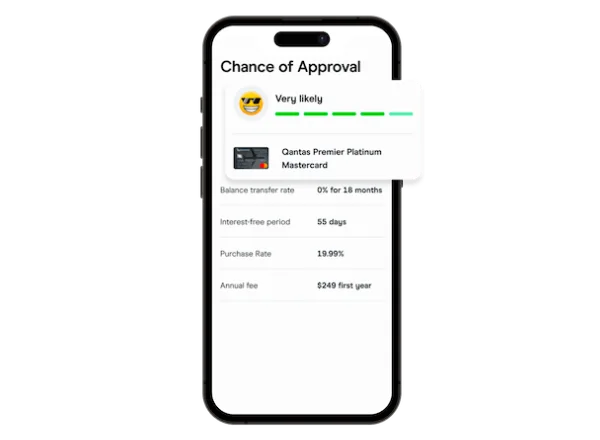
credit cards, insurance, utilities and more.
Ready to get
the Finder app?




 Trusted by over 500,000 Aussies
Trusted by over 500,000 Aussies




Finder Wallet is not a bank. Terms and conditions apply. Crypto trading products are made available in the Finder App, powered by Finder Wallet Pty Ltd, an AUSTRAC registered Digital Currency Exchange (DCE). Trading and holding cryptocurrency has a high level of risk. Cryptocurrency is a volatile asset class. You can incur losses. You should only trade cryptocurrency or related products if you fully understand, and agree to, the risks. We suggest you seek independent financial advice prior to accessing our services.
Read more on Finder App
-
Finder Stickers
We're giving away FREE limited-edition Finder Stickers, but they're only available in limited quantities, so don't miss out.
-
Money confession – I stole money from work… and never got caught
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money confession – I’m broke as a joke
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money confessions – My 40k shame
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money confessions – My SIL propositioned me
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money confessions – I’ve hidden huge debts from my husband
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money confessions – I’m addicted to eating out
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money confessions – Frugal friends
Straight-up advice on your biggest financial dilemmas and money confessions - when you're not sure of your next step, our experts are!
-
Money Confessions – I lent my brother $20k – help!
Straight-up advice on your biggest financial dilemmas - when you're not sure of your next step, our experts will tell you what to do!
-
Money Confessions – Bridezilla or fair call?
Straight-up advice on your biggest financial dilemmas - when you're not sure of your next step, our experts will tell you what to do!



