Cryptocurrency security: End to end guide on keeping your crypto safe
Your crypto is only worth something if you don’t lose it. Here’s how to keep it safe from start to finish
 This guide is sponsored by CoinSpot, the only Australian-based crypto exchange certified to the standards of both Blockchain Australia and ISO27001, the international standard for information security. CoinSpot also helps you improve the security of your account with 2FA, custom withdrawal restrictions and session timeout limit settings. Learn more.
This guide is sponsored by CoinSpot, the only Australian-based crypto exchange certified to the standards of both Blockchain Australia and ISO27001, the international standard for information security. CoinSpot also helps you improve the security of your account with 2FA, custom withdrawal restrictions and session timeout limit settings. Learn more.
Although they used to be common, cryptocurrency thefts and exchange hacks are now quite rare. This is due to enormous improvements in cryptocurrency security over time. For end users these improvements mean it's now possible to keep your cryptocurrency relatively safe without any kind of cybersecurity expertise, just by following some simple precautions.
This guide is a simple, non-technical explainer of what these kinds of precautions are and how to use them to help keep yourself safe at every step of the cryptocurrency journey.
If you plan on doing any buying and selling, a natural first step is knowing how to pick a safe cryptocurrency exchange.
Choosing a safe cryptocurrency exchange
It’s always important to choose a safe cryptocurrency exchange, but it’s especially important if you plan on leaving funds on the exchange for any period of time.
A safe exchange is one that you can trust to store private keys, to remain in business and to provide the reliability you need.
Here are five things to look for to get an overview of how safe a cryptocurrency exchange is.
1. Track record
Has the exchange ever been robbed or suffered a data breach? It’s not necessarily a deal-breaker if it has, but it’s not a good look either.
As far as is publicly known, most prominent Australian exchanges, including CoinSpot, have never been hacked.
2. Verification requirements
As a rule of thumb, exchanges that handle fiat (AUD, USD, etc) to cryptocurrency sales are required to verify their customers’ identity.
While some people prefer anonymity, which also provides security of a sort, you should be wary when dealing with no-ID exchanges, especially if you anticipate needing to recover lost passwords or change your 2FA.
All major Australian exchanges require user identification.
3. Regulation
Beyond verification, it’s helpful to ensure that your chosen exchange is operating in compliance with other regulatory requirements. In Australia, one of the big requirements is that cryptocurrency exchanges must be registered with AUSTRAC.
While non-registration is a red flag, you should know that registration isn’t necessarily a green flag. AUSTRAC registration does not mean an exchange has been approved, checked or otherwise credentialed in any way. If you see a cryptocurrency exchange trying to imply that AUSTRAC registration is some kind of regulatory stamp of approval which guarantees safety, rather than a bare minimum legal obligation, that’s also a red flag.
It can also be a good idea to look for exchanges that are certified under the Blockchain Australia Code of Conduct, as CoinSpot is.
Certification under the Code of Conduct is valuable confirmation that CoinSpot has adhered to best-practice standards through a rigorous external auditing process."
"The Australian Digital Currency Industry Code of Conduct establishes best-practice standards for digital currency businesses in Australia," explained Blockchain Australia CEO Steve Vallas.
"Businesses which are certified under the Code of Conduct offer peace of mind to consumers as they have passed an independent external audit process and successfully demonstrated compliance with these standards."
We commend Coinspot for undertaking this process. Certification under the Code of Conduct is a valuable confirmation that CoinSpot has adhered to best-practice standards through a rigorous external auditing process," Vallas said.
4. Age, popularity and reputation
The older a cryptocurrency exchange is, the more experience it has securing user funds. The more popular a cryptocurrency exchange is, the more funds it’s probably securing.
It’s reasonable to assume that there’s safety in numbers, so age and popularity can be helpful proxies for security.
According to SimilarWeb, CoinSpot is the most popular cryptocurrency exchange in Australia. It was founded in 2013, at around the same time as several of Australia’s most venerable exchanges.
5. Security features
Most cryptocurrency exchanges these days have solid security practices because those that don’t tend not to last long.
Standard practices that you’ll see at most good exchanges these days include holding the majority of customer funds in offline storage and using multi-signature wallets (wallets which need multiple keys to unlock) to prevent one person from pulling off an inside job.
For more assurance beyond that, you can look for exchanges that have additional security-related credentials such as ISO27001. Cryptocurrency exchanges with this certification have passed auditing for information security management.
This certification is a sign that exchanges have not only received expert approval, but also that they’re actively investing in improving their own security.
CoinSpot was the first Australian exchange to get ISO27001-certified, and today remains one of the relatively few cryptocurrency exchanges in the world with this certification.
Don't fall for the technobabble
Every crypto exchange likes to boast about its security and technical chops, but that boasting often doesn’t mean much. Sometimes it’s even complete gibberish.
For example, ill-fated Canadian cryptocurrency exchange QuadrigaCX, which abruptly took $200 million of customer funds to the grave, boasted on its website about security features such as “collective intelligent threat detection”.
However, if you do a Google search of the phrase, it becomes apparent that this is a completely made up term that almost no one except QuadrigaCX has ever used, and that it doesn’t actually mean anything.
If you find an exchange that’s trying to sell you with technobabble like “collective intelligent threat detection” or “dual gateway exchange platform”, it’s worth searching for the term online and seeing what, if anything, it actually means. Don't be afraid to search the internet for unfamiliar terms, because if an exchange's security credentials are just technobabble, that's a good red flag.
How is cryptocurrency stored?
Every single unit of cryptocurrency in existence is held in some kind of cryptocurrency address. This is the only way that cryptocurrency can be stored. So when someone says that they own cryptocurrency, what they’re really saying is that they own the keys to unlock certain cryptocurrency addresses and access the crypto inside.
These keys, typically referred to as “private keys”, are what you’re trying to keep safe. When you download and use a cryptocurrency wallet, your private keys will often end up living on whichever device you downloaded it to.
The private keys are the only thing a thief needs to steal cryptocurrency. They don’t need to know the corresponding address, and the irreversible nature of cryptocurrency transactions means that your crypto is as good as gone if the wrong person gains access to your private keys.
At the end of the day, cryptocurrency security is all about trying to protect those keys, while cryptocurrency theft is all about trying to find ways of getting at them, either directly or indirectly.
From a security perspective, cryptocurrency exchanges and wallets are all about putting layers of security between the private keys and the end user in a way that balances security with user-friendliness.
What do private keys look like?
Private keys are just snippets of data, primarily intended to be read by machines. They can be expressed in a few different ways.
Bitcoin private keys, for example, can be written out as 256-bit binary numbers – meaning a 256-character long string of ones and zeros. Or they can be expressed in 64 characters in hexadecimal.
Fortunately, keys can be expressed in more human-friendly forms as well. The simplest and most widely-used variation, favoured by most cryptocurrency wallets, is private keys expressed as 12 or 24 everyday words.
You will typically be given this phrase when setting up a new cryptocurrency wallet.
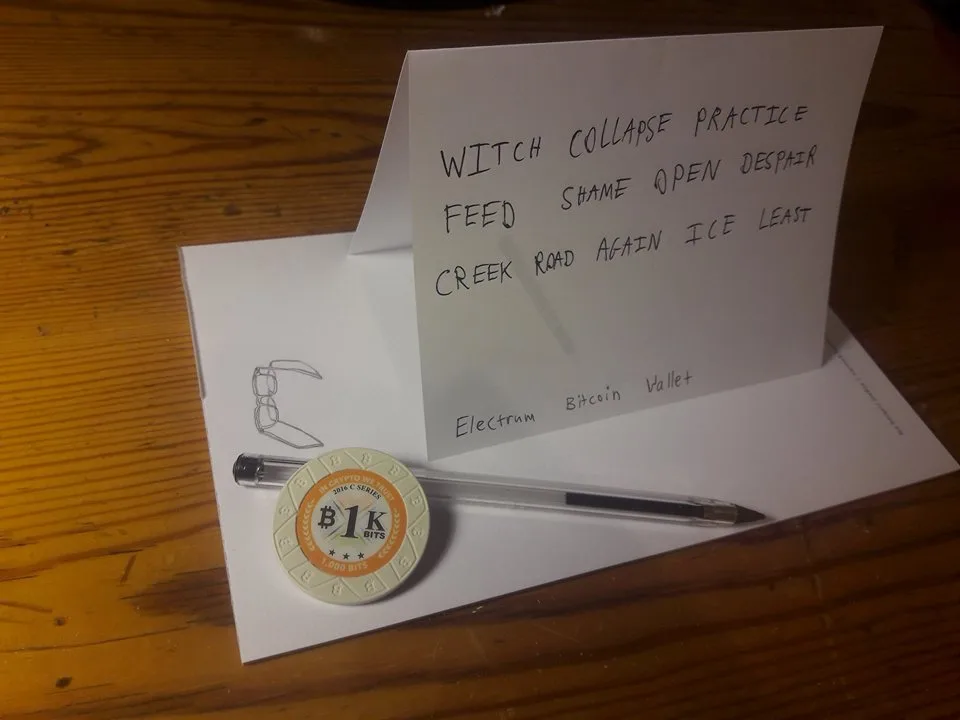
For example
In this format, as long as you keep track of your words, in the correct order, you will always be able to access your cryptocurrency.
This 12-word format is usually called a “seed phrase” or a “backup”, since it’s typically used as a last resort to restore your keys in case your wallet devices are lost. Conveniently, it can also be used as a single “master key” for multiple private keys, letting you access many different cryptocurrencies with the one phrase.
However, if anyone else gets access to those words, they can steal your cryptocurrency, and if you lose those words as well as any devices storing your private keys, you’ll probably also lose your cryptocurrency for good.
As you can imagine, storing private keys is a bit unconventional and risky in its own way. A lot of money has probably been lost over the years due to private keys being written on paper and then lost to floods, housefires, playful dogs and other disasters.
So unsurprisingly, even though taking personal custody of keys is widely regarded as the safer choice, many people still feel more comfortable entrusting their private keys to third parties such as cryptocurrency exchanges, registered custodians or certain banks.
In essence, this means protecting your keys with more traditional security measures like website logins, passwords and identity verification, while trusting that the third party is also taking suitable precautions to protect your keys.
There’s no single best way of storing private keys, but no matter how you’re storing your crypto, thinking about it from the perspective of protecting your private keys can help you understand your risks at any given time, and how certain precautions can protect your crypto.
Securing your devices and accounts
Given the potentially high stakes involved in cryptocurrency security, it’s well worth practising a bit of security hygiene before creating an account with a cryptocurrency exchange or downloading a personal wallet to your device.
Before you begin:
- Check that your email is safe. Has your email been compromised? You can try searching for your email address on haveibeenpwned.com to see whether your email and/or password has been given away in any previous data breaches. You might be unpleasantly surprised. It’s safer to avoid using compromised email addresses and passwords when signing up to a crypto exchange.
- Avoid reusing passwords. If possible, avoid using the same password for crypto exchanges (and wallets where applicable) as you’re using elsewhere.
- Set up your devices. Make sure your devices are ready for the responsibility of handling crypto. PCs should be periodically checked with virus and malware scans, and phones should have the latest manufacturer updates. And as always, avoid clicking on suspicious links. If practical, you may want to consider using separate logins, passwords and devices specifically for crypto.
Also, resist the urge to send any cryptocurrency to Nigerian princes.
After you begin:
- Beware of public Wi-Fi. Avoid logging into crypto exchanges or otherwise entering sensitive information over public Wi-Fi networks, such as those found in cafes, hotels, airports and the like. They cannot be trusted.
- Beware the Internet in general. There is no good reason to enter your private keys directly into a website, or to enter your crypto exchange login details anywhere except the exchange’s website. Avoid emailing yourself a copy of your private keys, or otherwise putting them on an internet connected PC.
And at any time, it’s important to make sure you’ve set up effective two-factor authentication (2FA) across all your important accounts.
Setting up effective 2FA
2FA is a system for better securing most types of online accounts, such as social media accounts, Google accounts and cryptocurrency exchange accounts.
It’s one of the most effective ways of securing your cryptocurrency exchange account and should be considered a must.
When you enable two-factor authentication, you will be required to authenticate online actions – such as making a withdrawal from a cryptocurrency exchange – in multiple places before it goes through. For example, when signed into a cryptocurrency exchange on your PC with 2FA enabled, you may have to confirm crypto withdrawals on your phone’s authenticator app first.
This can be extremely effective at preventing hacks because it requires thieves to have access to multiple logins, passwords or devices before they can do anything. For this reason, most reputable crypto exchanges make 2FA mandatory for all users.
Not all 2FA is equally suitable for cryptocurrency though, so it’s well worth making sure you’re doing it right.
Good vs bad 2FA
Reliance on SIM card-based 2FA, which depends on mobile phone numbers, has led to a lot of cryptocurrency thefts. It's been proven to be bad 2FA for cryptocurrency. Fortunately, there are better alternatives available.
Using a personal hardware wallet
It’s widely accepted that taking personal control of your private keys is safer than entrusting your crypto to an exchange. Indeed, you’ll often see exchanges themselves advising you to not keep funds there.
This is because exchanges are rich targets – so they’re constantly fending off attacks – and because they need to strike a delicate balance between accessibility and security.
By contrast, taking personal control of your crypto could make you less of a target while also letting you make security arrangements that you’re personally comfortable with.
That’s where hardware wallets such as the Ledger Nano or Trezor series come in.

Ledger Nano S (left), Ledger Nano X (right)
Hardware wallets are widely considered the gold standard of personal cryptocurrency storage.
They’re essentially offline lockboxes for private keys. You keep your keys in the device and then interact with crypto applications through the paired wallet app. Whenever you need to sign off on a transaction, you do so through the hardware wallet.
The main upshot of this is that it lets you keep your private keys entirely offline all the time, which isn’t usually possible with other wallet applications.
That said, some newer mobile devices have similar functionality. For example, iPhones supporting iOS 13+ onwards and Samsung phones from the Galaxy S10 onwards allow for offline private key storage in secure enclaves in the phone, with a similar result of keeping your private keys offline.
So if you don’t want to buy a hardware wallet, a good phone can also be a reasonably secure stand-in. Of course, carrying your crypto out into the world on your phone also means exposing it to many more new risks, so if security is your priority, there’s still no substitute for a hardware wallet.

Backing up your keys
The last line of crypto defence is your recovery phrase or seed phrase. This is the aforementioned collection of 12 to 24 words which underpins your private keys. It’s used to recover your funds if (and when) the devices holding your private keys die or get lost.
It’s essential that your seed phrase is kept in a safe place and that it’s kept secret.
Given the importance of these recovery phrases, many people don’t feel comfortable just writing them down on paper, and instead opt to engrave them in steel or titanium using products like Cryptosteel, Billfodl and Cryptotag.

Although they’re all a bit different, most of these backup devices are quite straightforward. Their only function is to legibly record up to 24 words in a certain order, while remaining as close to indestructible as possible.
Cryptosteel, for example (pictured below), allows you to arrange your words in a frame with steel letter tiles and then lock the frame.

Locking up the crypto and not throwing away the key
Once it’s set up, what you do with your backup device(s) is strictly your business, as long as it’s safe.
It’s kind of funny how a very tangible chunk of metal ends up being one of the best abstractions of a digital currency.
Although there are never any guarantees, whether you prefer to just leave your funds on a reputable exchange, withdraw them to a personal wallet, use a personal wallet backed up with a cold, hard recovery seed, split your keys up or just store your keys in different places as the mood takes you, there are precautions you can take at every step to improve your security and keep your funds safe.
Trade with CoinSpot
Compare cryptocurrency exchanges here
Compare other products
We currently don't have that product, but here are others to consider:
How we picked theseLatest cryptocurrency news
-
The Coinstash Cryptocurrency Hub
30 May 2024 |
-
Ordinals and runes – the new crypto craze?
24 Apr 2024 |
-
Join the party: Finder’s giving away $200K worth of Bitcoin
23 Feb 2022 |
-
Australians have spent $50.9 million on crypto trading fees
31 Jan 2022 |
-
Stablecoins vs Bitcoin: What’s the difference?
3 Nov 2021 |
Disclosure: The author holds cryptocurrencies including LINK at the time of writing
Picture: Shutterstock

